-
Understanding DevSecOps
Understanding DevSecOps DevSecOps (Development, Security, and Operations) is an evolution of the DevOps methodology that integrates security practices into every phase of the software development lifecycle (SDLC). The core idea behind DevSecOps is to make security a shared responsibility, seamlessly integrated into the development process… [ Read More ]
-
Describing SQL injection attack
Describing SQL injection attack SQL Injection Attack SQL Injection (SQLi) is a type of attack that targets web applications by exploiting vulnerabilities in an application's software that interact with databases. It occurs when an attacker manipulates an SQL query by injecting malicious SQL code into… [ Read More ]
-
Learning about the Secure DevOps
Learning about the Secure DevOps DevOps is a set of practices, tools, and cultural philosophies that aim to improve the collaboration between development (Dev) and IT operations (Ops), streamlining the software delivery process and enabling more efficient, faster, and continuous development cycles. However, as the… [ Read More ]
-
All you ever need to know while connecting to Virtual machine on Azure
In Azure, there are several ways to connect to a Virtual Machine (VM) depending on your requirements, security policies, and the operating system (Windows or Linux) of the VM. Here are the key methods for connecting to a VM. Remote Desktop Protocol (RDP) for Windows… [ Read More ]
-
Learning Path review questions: LP05
Learning Path review questions 01. What benefits can you achieve by modularizing your infrastructure and configuration resources? Modularizing infrastructure and configuration resources in Infrastructure as Code (IaC) offers several key benefits: Reusability: You can reuse modules across different projects, environments, or teams. This reduces duplication… [ Read More ]
-
Implementing DSC and Linux Automation on Azure
Implementing DSC and Linux Automation on Azure In Azure, you can use Azure Automation to implement Desired State Configuration (DSC) for both Windows and Linux environments. DSC is a powerful mechanism for ensuring that your infrastructure is configured correctly and remains compliant with the desired… [ Read More ]
-
Examining DSC Configuration File
Examining DSC Configuration File In Desired State Configuration (DSC), a configuration file defines the desired state of a system. The configuration file is written in PowerShell and is composed of several key elements that instruct the system on how to achieve and maintain the desired… [ Read More ]
-
Exploring Azure Automation State Configuration (DSC)
Exploring Azure Automation State Configuration (DSC) Azure Automation State Configuration is a service within Azure Automation that enables you to manage and enforce Desired State Configuration (DSC) across your Azure infrastructure. It helps automate the configuration of both Windows and Linux machines and ensures that… [ Read More ]
-
Gain insight into the Desired State Configuration (DSC)
Gain insight into the Desired State Configuration (DSC) Desired State Configuration (DSC) is a configuration management framework built into Windows PowerShell that enables IT administrators to define and manage the desired state of their infrastructure. DSC ensures that systems are configured in a consistent, predictable,… [ Read More ]
-
Understanding Configuration Drift in DevOps
Understanding Configuration Drift in DevOps Configuration drift refers to the phenomenon where the configuration of systems or resources gradually changes over time, often unintentionally, and diverges from the desired or defined configuration state. This can happen in a variety of environments, including on-premises, hybrid, and… [ Read More ]
DevOps, Cloud, Azure resources & blog
Author: Rajnish Kumar Jha
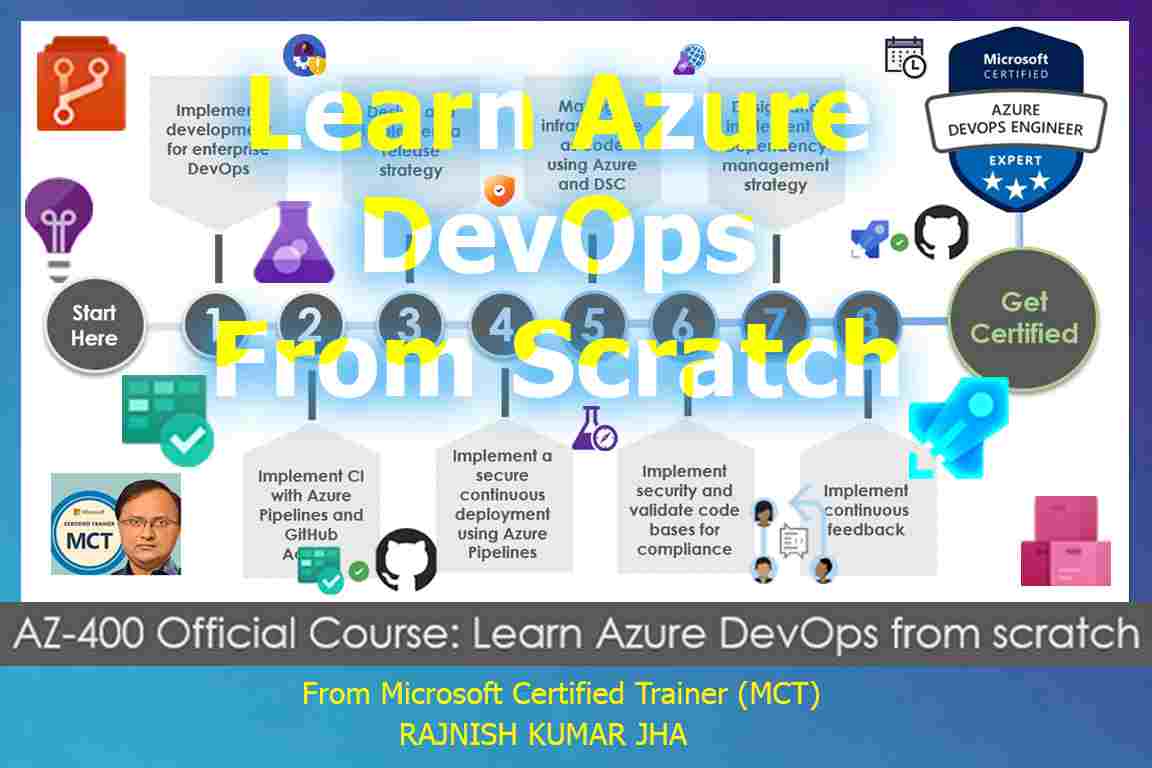
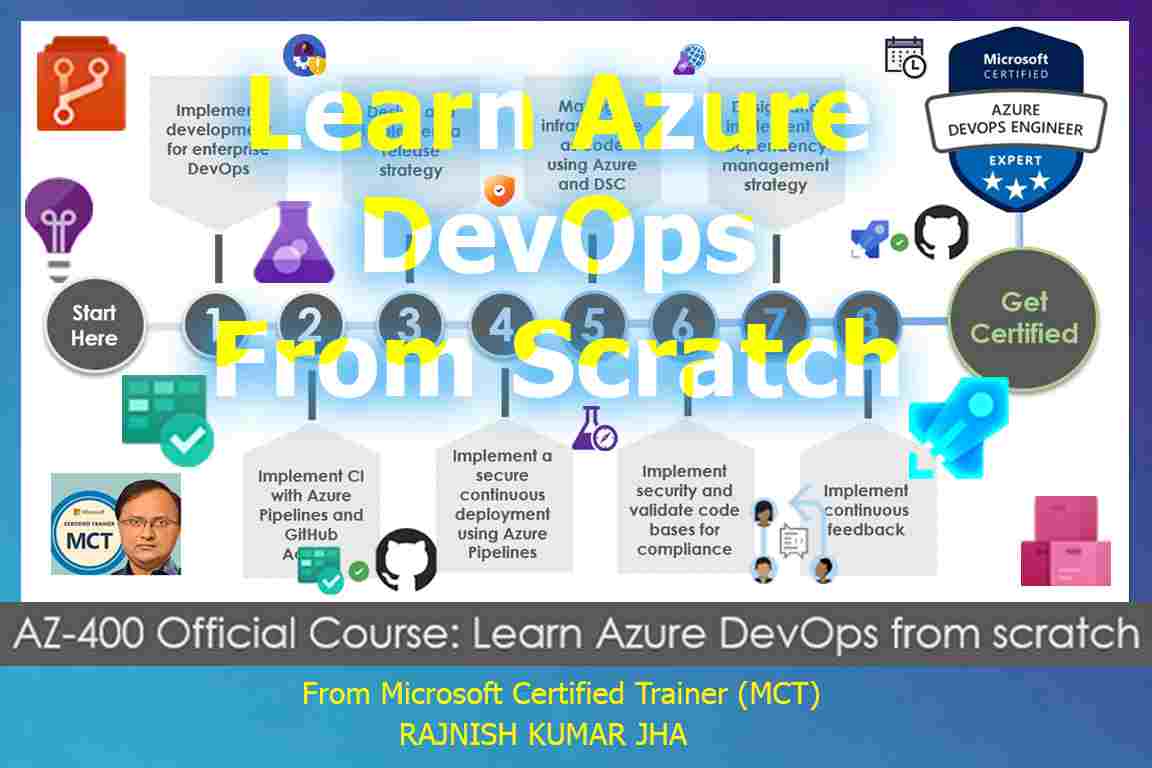
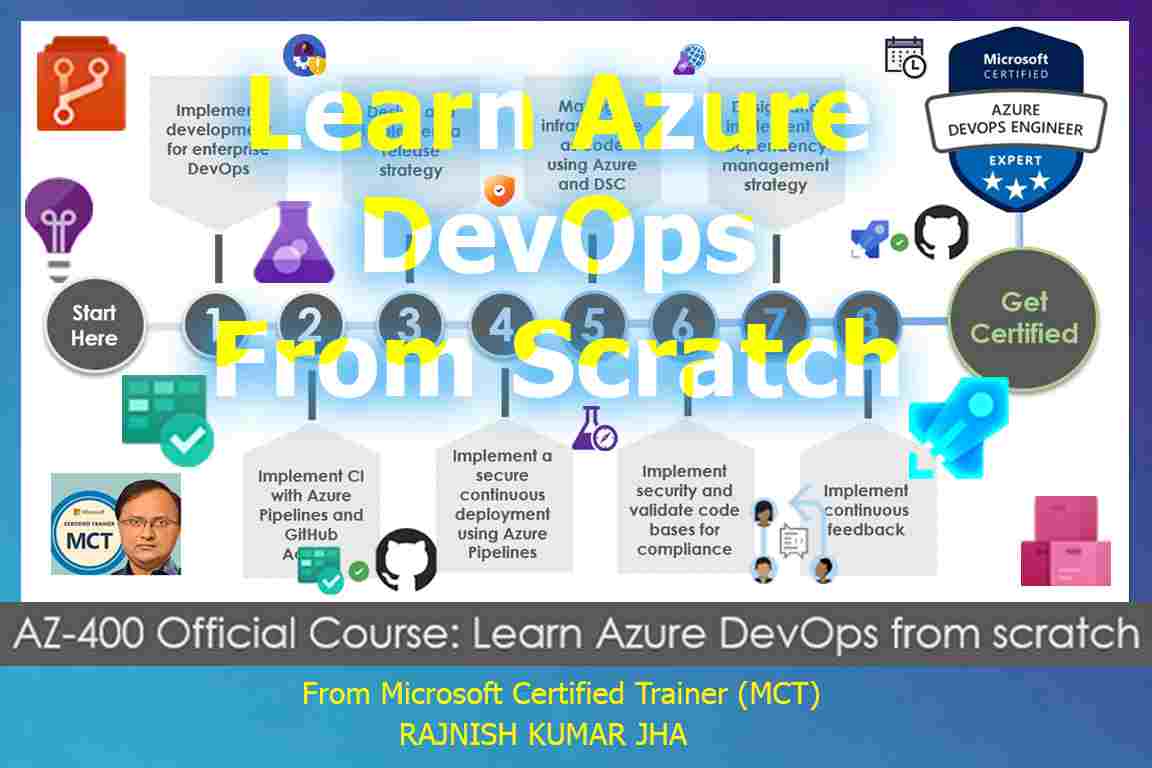
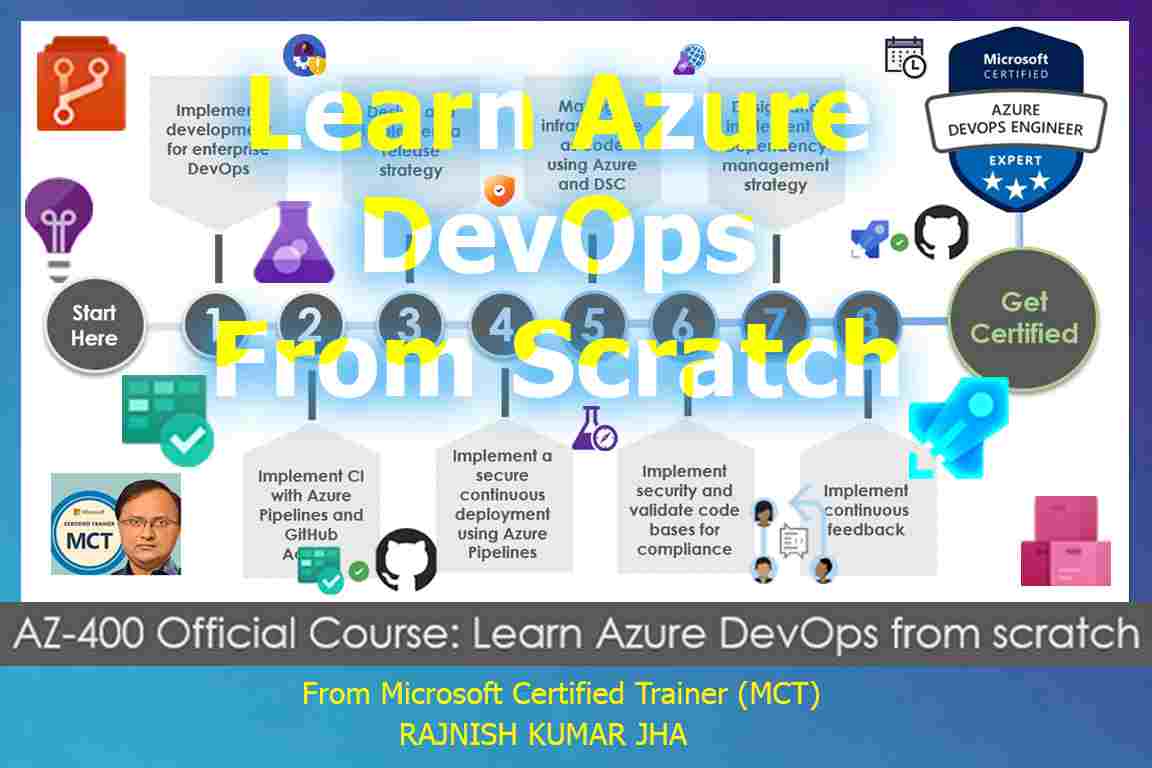
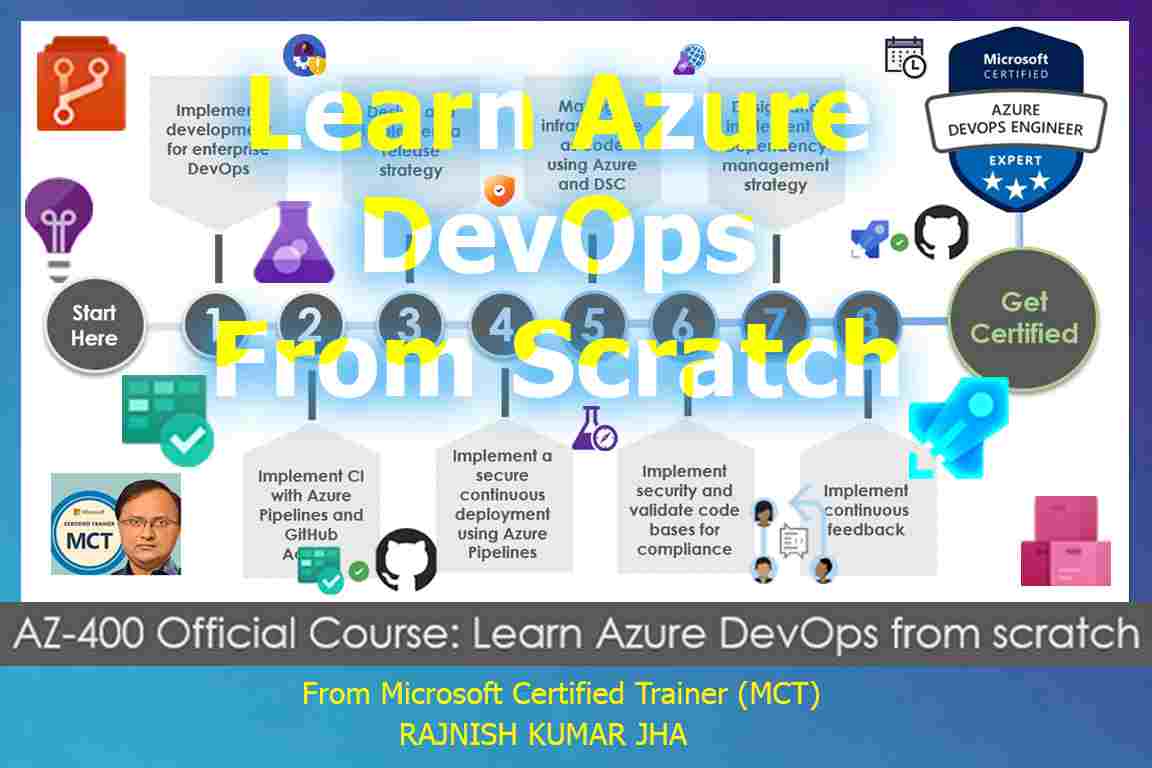
Featured Courses

Rajnish Kumar Jha
MCT, MCSA, MCSE, MCAD, MCPD, MCTS, MCSD
My name is Rajnish Kumar Jha. I am Technical architect on Azure Cloud and .NET since 21+ years. I’ve worked for pioneer companies and as freelance trainer/consultant helping my clients to achieve their IT goals.
I find blogging, a great way to share back what I’ve learned all through my professional journey. You are welcome to connect or share feedback/suggestion here or through an email.
Popular Posts
Stay Connected
Unlock the full potential of Azure Cloud with me
– Your trusted guide to Azure mastery!
SUBSCRIBE
My newsletter for exclusive content and offers. Type email and hit Enter.
No spam ever. Unsubscribe anytime.
Read the Privacy Policy.