-
Understanding Microsoft Defender for Identity
Understanding Microsoft Defender for Identity Microsoft Defender for Identity (formerly known as Azure Advanced Threat Protection (ATP)) is a cloud-based security solution that helps detect, investigate, and respond to advanced threats, compromised identities, and malicious insider actions. It is part of the Microsoft Defender suite,… [ Read More ]
-
Azure Bicep explained in detail
Azure Bicep is a powerful and modern domain-specific language (DSL) designed to simplify the process of defining Azure resources and automating their deployment using Infrastructure as Code (IaC) principles. It serves as an abstraction layer over Azure Resource Manager (ARM) templates, providing a simpler, more… [ Read More ]
-
Exploring Azure Resource Locks
Exploring Azure Resource Locks Azure Resource Locks are a critical feature used to protect Azure resources from accidental or unauthorized changes, deletions, or modifications. They help ensure that important resources remain stable and unchanged, particularly in production environments where any modification or deletion could lead… [ Read More ]
-
Exploring Azure Policy and CI/CD pipeline integration
Exploring Azure Policy and CI/CD pipeline integration . ✏️[!NOTE] Three slides combined Explore Azure Policy Understand policies Explore initiatives` ' Azure Policy Overview and Integration with CI/CD Pipeline in Azure DevOps Azure Policy is a key governance tool that allows organizations to enforce rules and… [ Read More ]
-
Examining Microsoft Defender for Cloud usage scenarios
Examining Microsoft Defender for Cloud usage scenarios 'OR ### Microsoft Defender for Cloud Usage Scenarios Let’s break down two practical usage scenarios that highlight how Microsoft Defender for Cloud can be leveraged in real-world environments. Scenario 1: Incident Response (Detect, Access, Diagnose) Situation: An organization… [ Read More ]
-
Exploring Microsoft Defender for Cloud
Exploring Microsoft Defender for Cloud Microsoft Defender for Cloud (formerly known as Azure Security Center and Azure Defender) is a comprehensive cloud security solution provided by Microsoft that helps organizations protect their workloads and resources across hybrid and multi-cloud environments. It offers advanced threat protection,… [ Read More ]
-
Implementing Pipeline Security in Azure DevOps
Implementing Pipeline Security in Azure DevOps Implementing pipeline security in a CI/CD pipeline is essential to ensure the integrity and security of your software delivery process. It involves securing access, managing permissions, ensuring proper authentication and authorization, and integrating dynamic scanning mechanisms to detect vulnerabilities… [ Read More ]
-
Interpreting alerts from scanner tools
Interpreting alerts from scanner tools Interpreting alerts from container and software composition analysis (SCA) tools involves reviewing reports that typically include various security vulnerabilities, license risks, compliance issues, and information about outdated libraries. While these alerts are vital for maintaining a secure and compliant software… [ Read More ]
-
Automating Container scanning
Automating Container scanning Automating container scanning in your CI/CD pipeline, including container image scanning, is critical for ensuring that your containers are secure, compliant, and free of vulnerabilities. This can be achieved by integrating various tools like Microsoft Defender for Cloud, Microsoft Defender for Containers,… [ Read More ]
-
A detailed guide on Azure Load Balancer
Azure Load Balancer: Overview Azure Load Balancer is a high-performance, fully managed Layer 4 (TCP/UDP) load balancing service provided by Microsoft Azure. It is designed to distribute incoming network traffic across multiple backend resources, such as virtual machines (VMs), virtual machine scale sets, or IP… [ Read More ]
DevOps, Cloud, Azure resources & blog
Author: Rajnish Kumar Jha
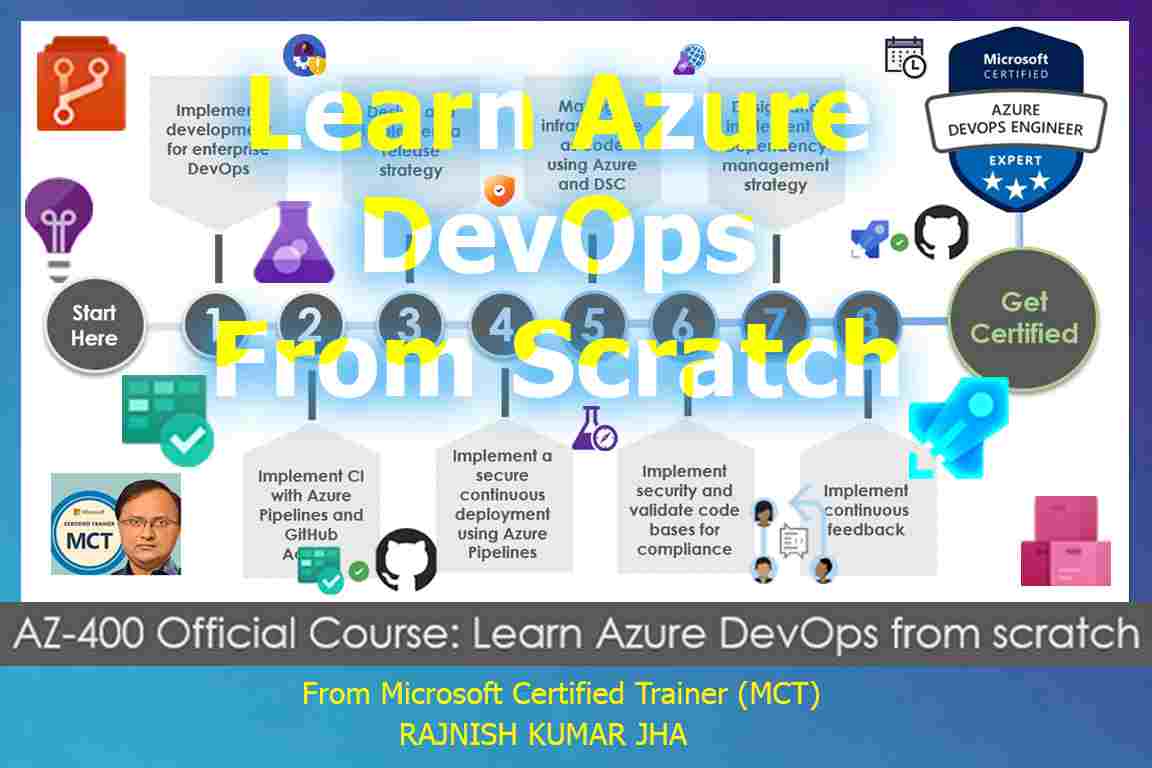
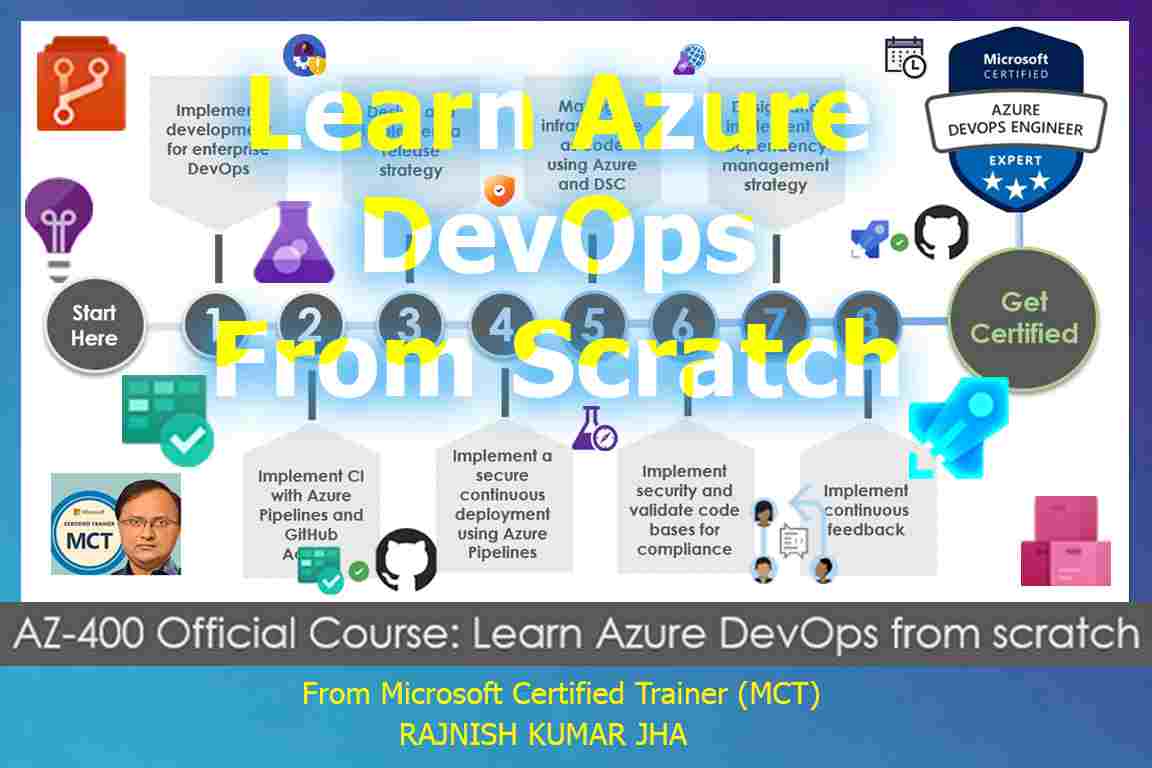
Featured Courses

Rajnish Kumar Jha
MCT, MCSA, MCSE, MCAD, MCPD, MCTS, MCSD
My name is Rajnish Kumar Jha. I am Technical architect on Azure Cloud and .NET since 21+ years. I’ve worked for pioneer companies and as freelance trainer/consultant helping my clients to achieve their IT goals.
I find blogging, a great way to share back what I’ve learned all through my professional journey. You are welcome to connect or share feedback/suggestion here or through an email.
Popular Posts
Stay Connected
Unlock the full potential of Azure Cloud with me
– Your trusted guide to Azure mastery!
SUBSCRIBE
My newsletter for exclusive content and offers. Type email and hit Enter.
No spam ever. Unsubscribe anytime.
Read the Privacy Policy.